WAF & DDoS Protection Indonesia
we provides an all-inclusive security solution for users concerned about website security in Indonesia
Web Application Firewall
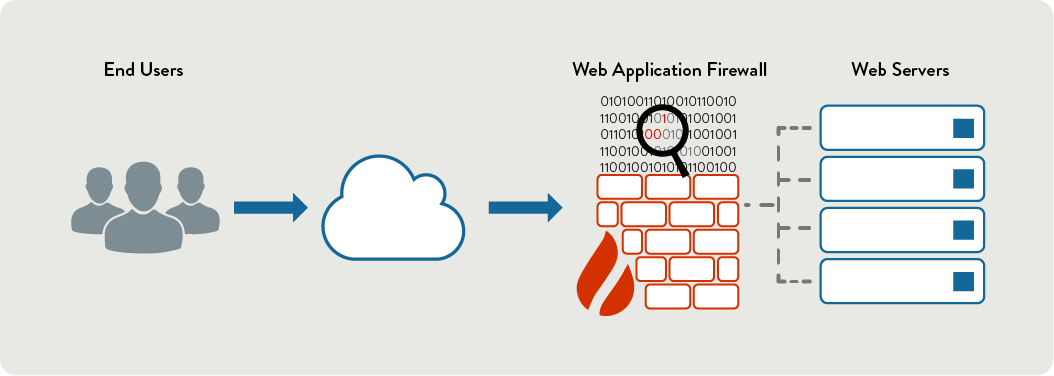
A Web Application Firewall (WAF) is an application firewall for HTTP applications. It applies a set of rules to an HTTP conversation. Generally, these rules cover common attacks such as cross-site scripting (XSS), SQL injections, session hijacking, brute force attacks, etc.
Jupiter enterprise level web application firewall protects your websites from unknown web attacks as well as known attacks with the highest precision.
Jupiter WAF not only detects known attack patterns via pattern-matching analysis, but also analyzes traffic for malicious behavior with two additional unique detection methods: Semantic analysis and Heuristic analysis. This allows our logic based analysis engine to detect known, unknown and even modified attacks with industry-leading accuracy.
Protect Your Website Against Web Attacks

OWASP Top Ten Vulnerabilities
Jupiter WAF protects against the top ten vulnerabilities identified by OWASP. To do this, we use 26 custom algorithms and rule sets which allow our WAF to detect and to accurately block web attacks with low false positives.
Our logic based algorithms allow our WAF to detect a wider range of web attacks. Thus, it even detects both known and unknown or modified web attacks.

Online Payment Compliance
Data leaks for small businesses result in heavy financial losses. All websites which a credit card payment module are required to comply with PCI-DSS 6.6 standards.
It is important to keep consumers’ credit card information and other personal information safe when exchanging information online.
NEED TO INTEGRATED YOUR CDN WITH WEB SECURITY
(CDN + Web Application Firewall + DDoS Protection + Free SSL)
???
DDoS Protection
Distributed denial-of-service (DDoS) attacks overload resources of a targeted system in various ways. Add your website to Jupiter DDoS Protection if you want us to monitor and block them in real-time.

What Types of DDoS Attacks are Blocked?
Our advanced DDoS solution (Layer 3, 4 & 7) protects against the most common one to sophisticated multi-vector and application layer attacks.
TCP SYN Floods
TCP FIN Floods
TCP RST Floods
HTTP GET Floods
HTTP Post Floods
HTTP XMLRPC PingBack attacks
TCP Fragment attacks
Slowloris
TCP Syn Spoofed
ICMP Floods
HTTP HEAD Floods
Brute Force
TCP Ack Floods
Ping of Death
DNS NXDomain Floods
HTTP Cache Control
HTTP SSL Saturation
Amplified DNS DDoS
RUDY
Smurf
Ask the experts
Our highly qualified staff will help you to get the right fit for your business.

